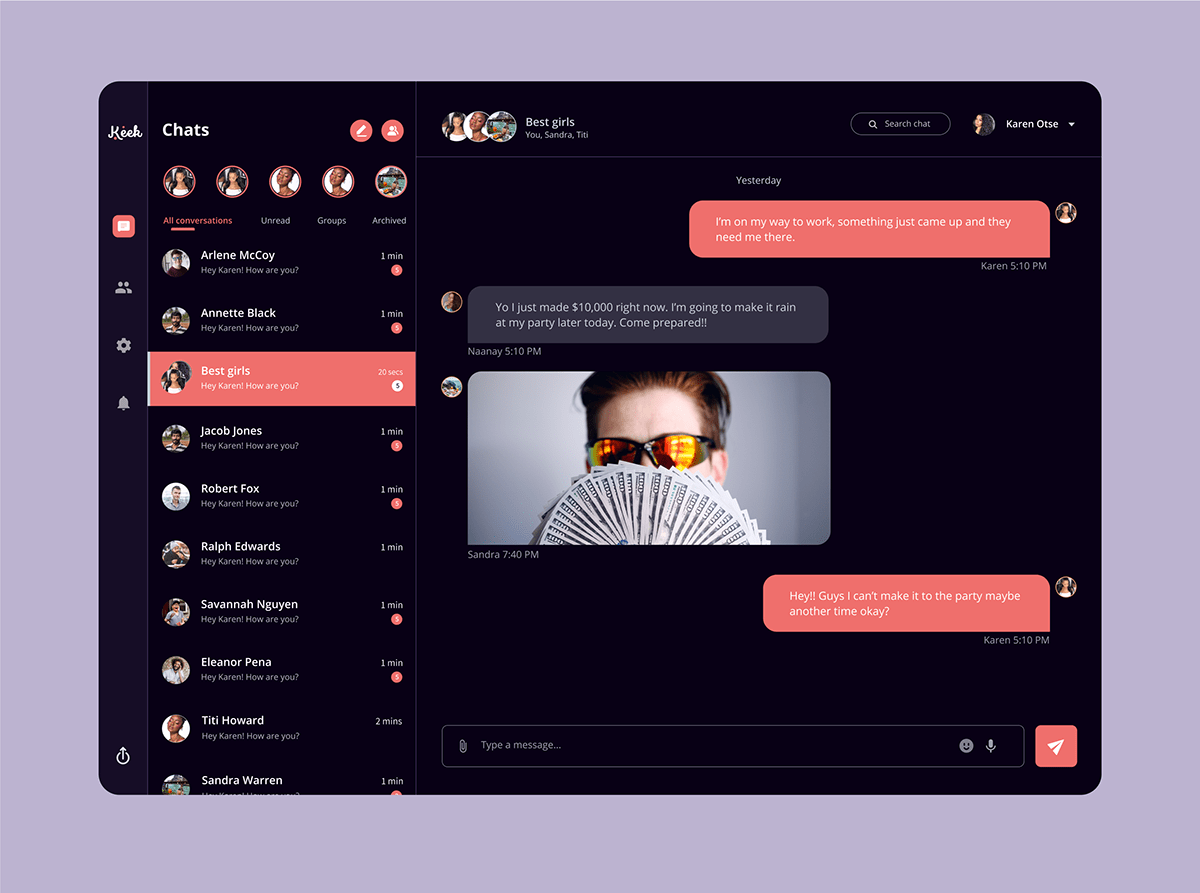
Find Dark Web Laptop stock photos and editorial news pictures from Getty Images. Select from 470 premium Dark Web Laptop of the highest quality. Step 3: Install the TOR browser bundle on your PC or Mac. When the download is complete, double-click deep web drug store the downloaded file, choose the. The challenge, though, is that you must know the website addresses you want to visit. The dark web doesn't have an index or ranking system. The dark web and how to access it. 1. First of all, go to Tor Project and download the Tor Browser. 2. Once you download it, install it like any other. These would add more layers of protection, but again, not fully safe. Additional additional precautions: Buy a burner laptop and pay as you go. It's possible that a hacker may have already compromised your security if they got your info from the dark web. Run a check with your antivirus software on your. Search from thousands of royalty-free "Dark Web" stock images and video for Get 10 free images. Computer haker sitting at the desk and using laptop. And voil, it's ready to go! Visit dark web sites by entering.onion URLs in the Tor Browser. See Useful Resources below to find URLs that.
And voil, it's ready to go! Visit dark web sites by entering.onion URLs in the Tor Browser. See Useful Resources below to find URLs that. Neither will deep web drug prices you be able to use your normal browser to access it. You will need a custom browser able to penetrate the layers of the deep web. In this June 19, 2024, file photo, a person types on a laptop keyboard. But some criminals buy names and passwords from the dark web and. Seems like modern routers allow you to block Tor calls which is how dark web is accessed. Of course if they are smart enough to get to the. Laptop Mag. You can get your code in 115 seconds... Prev post Internet of things vacancies in the medical industry were the hardest tech. 'Unfriended: Dark Web' review: Further laptop adventures turn too grim. By Katie Walsh. Chicago Tribune. Jul 19, 2024 at 12:22 pm. For most people, using Tor Browser is as simple as downloading it and running it, the same way you'd download Chrome or Firefox. If you've never used Tor,...Missing: laptop Must include: lapto. Get off your personal computer Don't connect from your internet address Encrypt your storage Use private search engines Communicate securely.
Although I seem to have deep web drug markets forgotten where it was, I was reading some blog post that said something like this: While browsing the dark web it is. 5 Best Laptops For Browsing The Dark Web Asus VivoBook E12 269 ASUS VivoBook 15 565 Lenovo Chromebook Flex 3 227 ASUS Chrome book. Plus, many of the best laptops have all-day battery life, whether it's office work, web browsing and research, or even lightweight gaming. Unlike an onion, slicing into the internet probably won't make you cry... but then again, we can't promise anything. Get urgent security alerts delivered to. Someone needs to get down there and interview the staff, I took his laptop and the dark web address down to Tech Support this morning. The Lenovo Chromebook is the best affordable 2-in-1 laptop for dark web, and it is an excellent choice for anyone looking to buy a new laptop. You can buy guns or drugs illegally on the dark web. Every device connected to the Internet including your laptop, smartphone, and tablet has an IP. What I would do is first make sure you have a great firewall in front of your network. For me I use a WatchGuard and I'm using Application.
Head back to the cafe and go to the work desk to repair the broken laptop. The player will now have access to the Dark Net. How To Work With Dark Web? Technically, it is not much difficult to access the dark web. By far, Tor is the simplest means to work with. In. Helping leadership understand the risks can make the case for funding to and skills when customer data goes up for sale on the dark web. For most people, using Tor Browser is as simple as downloading it and running it, the same way you'd download Chrome or deep web drug links Firefox. If you've never used Tor,...Missing: laptop Must include: lapto. It's an encrypted part of the internet, which means it hides your identity and location. Generally, you need to already know how to find certain. For anyone to access the dark web, a special type of software and web browser is required. The most well-known and frequently-used software is. Malware written in the Go language (aka Golang) has become common among threat actors. Based on dark web posts by a user named Qilin (who seems to be. The primary use of the dark web is for e-commerce. With the use of cryptocurrency, such as Bitcoin, users can make any purchase on the dark web without.
Darknet Onion Links Drugs
LI Man Charged With Selling Meth, Ecstasy Through Dark Web: Feds - Brentwood-Central Islip, NY - The 39-year-old sold the drugs through an encrypted messaging app how to get on the dark web on laptop using the screen name. If you have, then you’re probably wondering how one can access these hidden corners of the Internet. Tor works like magic, but the result is an experience that’s like the dark web itself: unpredictable, unreliable and maddeningly slow. The investigation was led by local German investigators with the participation of foreign authorities, including the FBI and Europol. Spurdomarkin kautta vakiintuneen politiikan mukaisesti, joka vallitsee toimittajien sääntöjä näistä asioista, jos ristiriitaisuuksia. The underground ecosystem represents a portion of cyberspace that is considered crucial for the business of criminal crews that specialize in fraudulent activities related to payment cards. Bitcoin Next Generation (Bitcoin-NG) is a Byzantine Fault Tolerant (BFT) blockchain protocol proposed and built by the founder of Ava Labs, Emin Gün Sirer, and several other leading computer scientists in an attempt to combat the perceived scalability and block size inefficiencies of the original how to get on the dark web on laptop Bitcoin network. The President hands off full control of the nation's missiles and other defense protocols to Colossus and makes the announcement to the world that he has ensured peace. Among other functions, compilers are commonly used to translate computerized code from high-level programming languages into simpler assembly languages that are able to decipher machine-readable instructions.
On our site you can always find the current link to this resource. To estimate the scale of encryption-signing, information hub activity, and seller migration, I downloaded and extracted data from key original sources using python and wget. These mass dustings may also be used as stress tests, where a large amount of dust is sent in a short amount of time to test the throughput, or bandwidth, of a network. The deep Web contains 7,500 terabytes how to get on the dark web on laptop of information compared to nineteen terabytes of information in the surface Web.